Threat Intelligence and The Pyramid of Pain
4.6 (400) · € 35.50 · In Magazzino
There is great interest among security technology and service providers about the intersection of global threat intelligence with local observations in the network. While there is certainly cause for excitement, it’s worth pausing to ask the question “Is Threat Intelligence being used effectively?”
TryHackMe: Pyramid Of Pain Writeup - Aleyna Doğan

Vulnerability Threat Intelligence
5 Steps to Effective Cyber Threat Intelligence Programs, Educational Guides

Leveraging EDR Data to Improve Cyber Threat Intelligence

Pyramid of Pain — Evolving our Defenses to Combat Supply Chain Attackers, by Yehuda Gelb, checkmarx-security

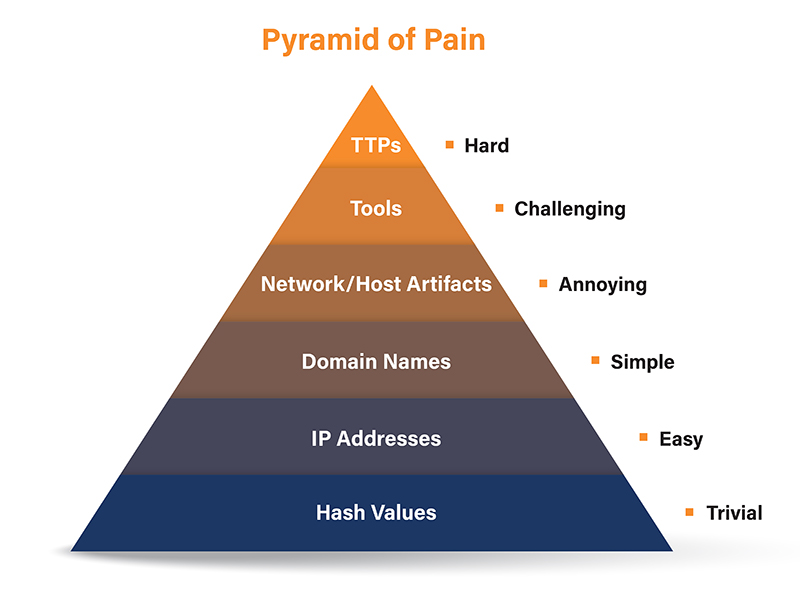
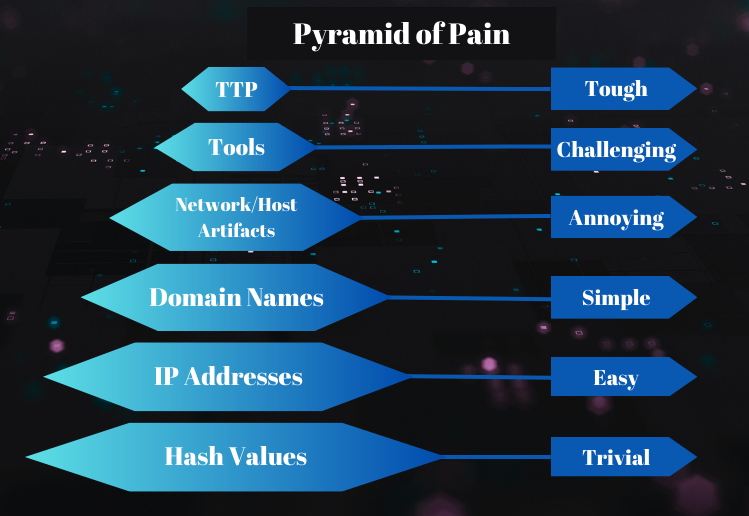
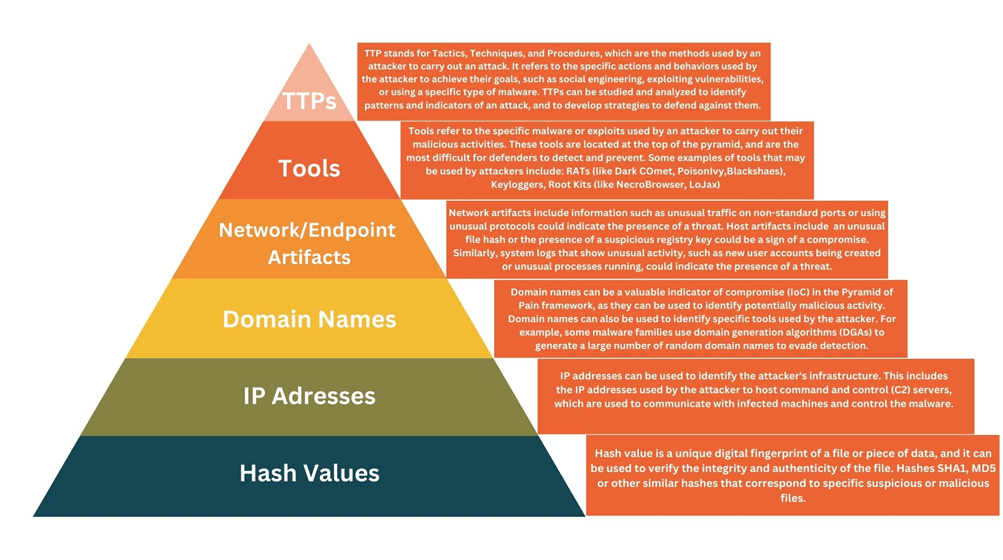
The Pyramid of Pain

What Is the Pyramid of Pain in Threat Detection? (CTIA)

EC-COUNCIL on X: David Bianco's #PyramidOfPain lists six indicators of cyberthreats, plus how much pain it causes an adversary when their plans are thwarted at each level. Sign up for the #CTIA
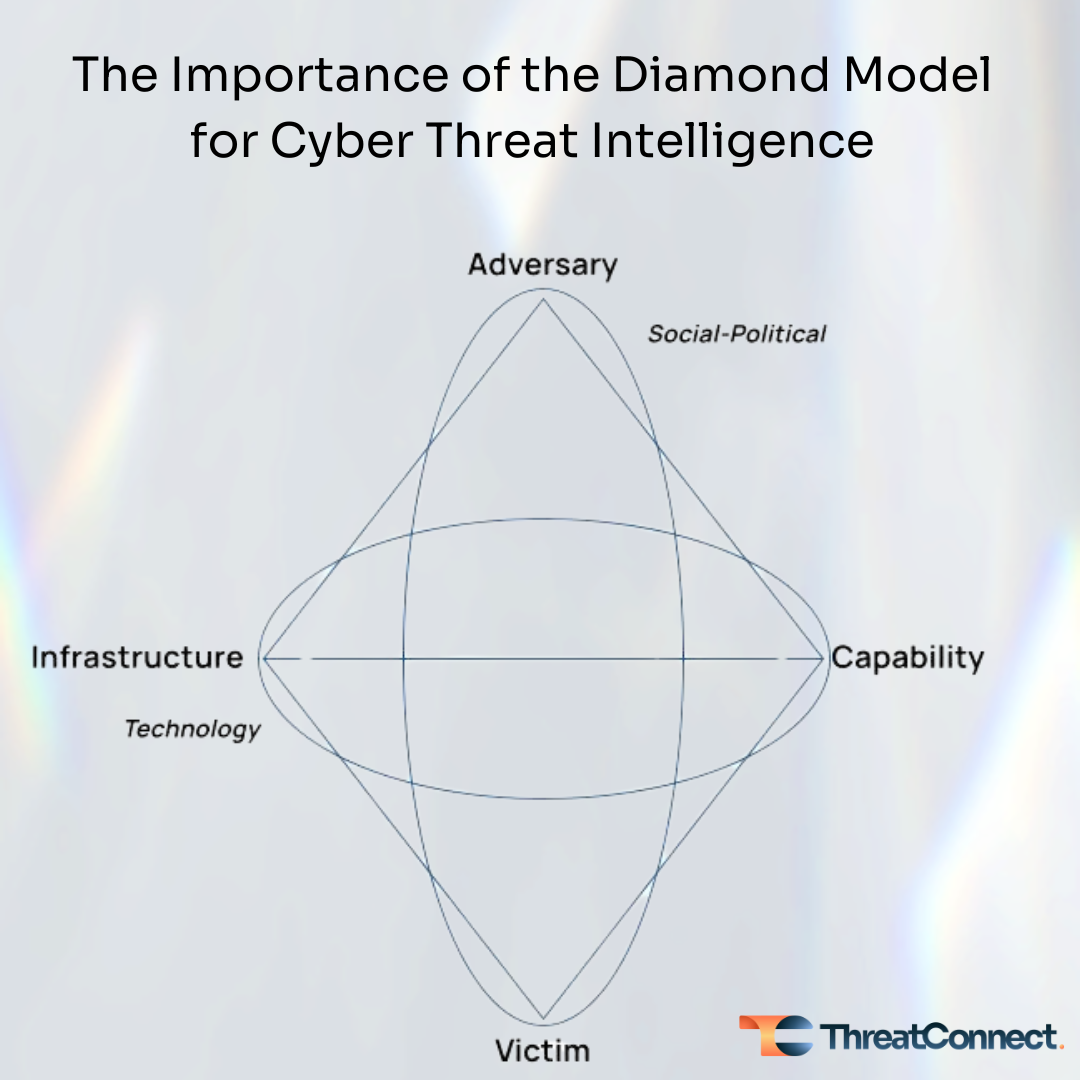
The Importance of the Diamond Model for Cyber Threat Intelligence
Pyramid of Pain with MSSPs : How SOC365 Can Help Organizations Prioritize and Operationalize Indicators of Compromise for Effective Cyber Defense

Pyramid of Pain — Evolving our Defenses to Combat Supply Chain Attackers, by Yehuda Gelb, checkmarx-security







