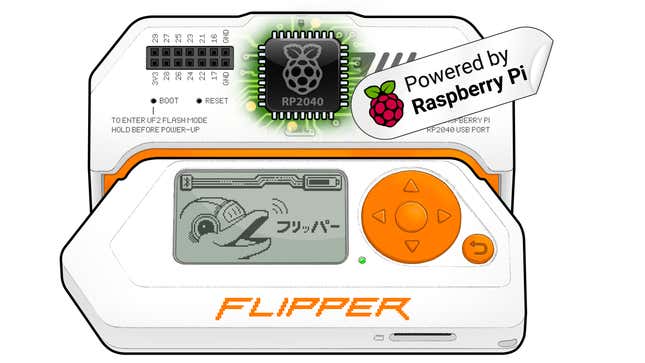
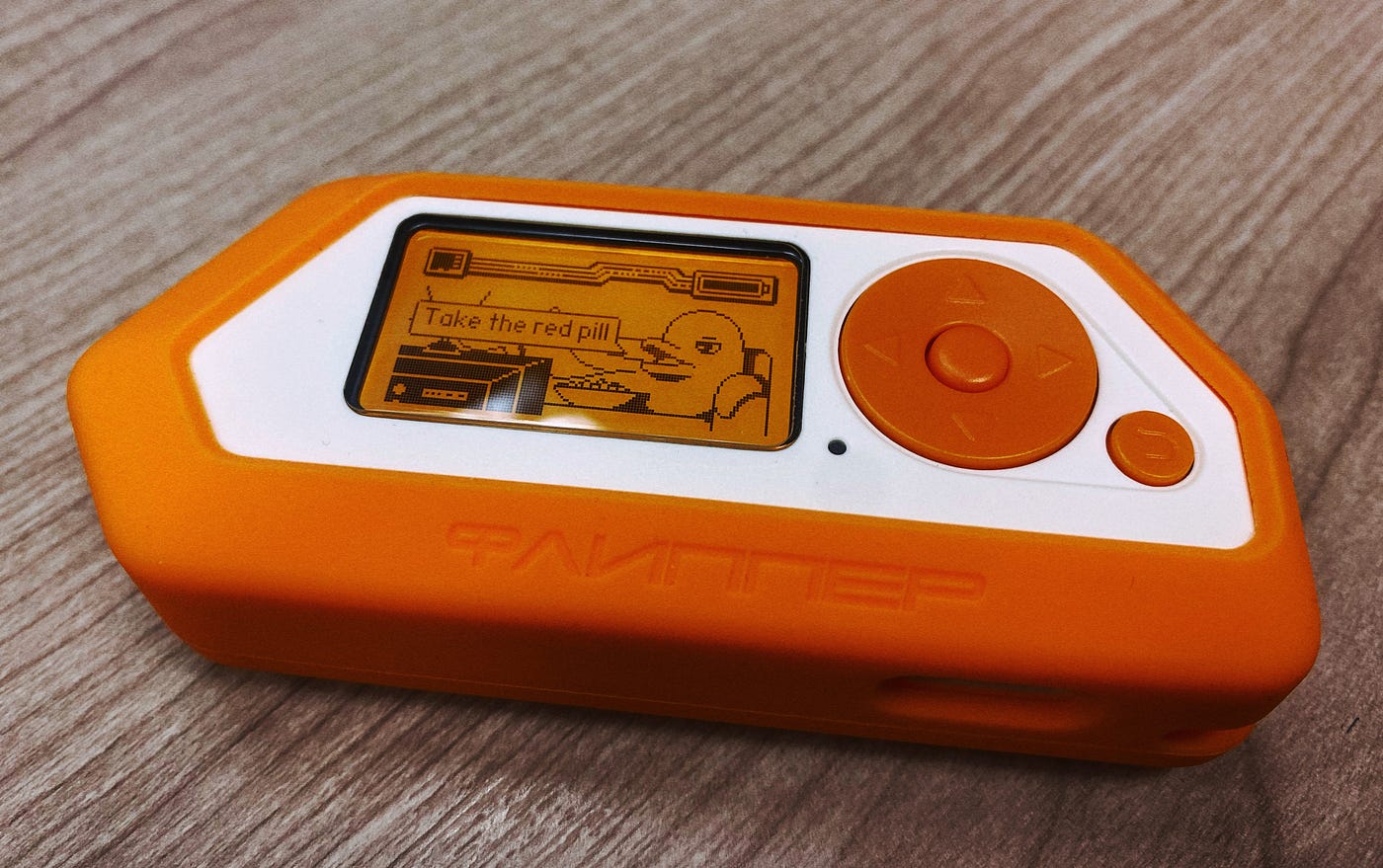
Exploring the Capabilities of Flipper Zero and Ubertooth One: Essential Tools for Wireless Security Testing (Part 1), by Jason Yee
4.8 (481) · € 31.00 · In Magazzino

Kali Linux with Virtual Box. I created this article based on the…, by Sophiecuruchet

Techniques used for Firmware reverse engineering, by GMQureshi

Apple TV3 Jailbreak. As we know Apple is one of the best…, by Margaret R. Harris

LINUX OPERATING SYSTEM. What is Linux?, by Muhammad Umer Kabir

Exploring the Capabilities of Flipper Zero and Ubertooth One: Essential Tools for Wireless Security Testing (Part 1), by Jason Yee

Scanning for Viruses on Mac: How to Do a Virus Scan?, by G. Berrios

Scanning for Viruses on Mac: How to Do a Virus Scan?, by G. Berrios

Hak5 WiFi Pineapple Mark VII: A Comprehensive Toolset for Wireless Network Security Testing and Penetration Testing (Part 2), by Jason Yee

5G and WIFI 6:. A tech revolution?, by ACM GITAM

Using SET to Simulate an Attack. We are going to have a look at the…, by Zuhayr Khalid

Scanning for Viruses on Mac: How to Do a Virus Scan?, by G. Berrios
Why Industries are Switching to Linux So Quickly, by Maas Mohamad Ali

Using SET to Simulate an Attack. We are going to have a look at the…, by Zuhayr Khalid
كبسة دجاج Unbearable awareness is